Our network works like this. We have our Roadrunner coming in to a Dlink DI-604 Router. From that router we have a US Robotics 8054 Wireless Access Point and Router running in AP mode, one network card in the server, and the wan port of another Dlink DI-604. This is my special wireless DMZ. Behind the second DI-604 I have all of the wired computer, the second network card in the server, and a Linksys WRT54G Wireless Access Point and Router also only being used as an access point. The linksys is new. Before we would connect to the US Robotics and then for wireless clients that needed special network access, we would VPN into the the server to get that access. The VPN access was a lot slower and had a tendency to get disconnected and you wouldn’t realize it or you would take your computer someplace and forget to reconnect to the VPN. I got the Linksys to run on the trusted network so I could have some wireless clients that are trusted connect to it and let the untrusted clients connect to the US Robotics but I needed a really secure solution for the trusted wireless network. I decided to use WPA with a Radius server using a User Certificate for authentication.
Server Setup
I got most of my setup information from this article, http://www.hansenonline.net/Networking/wlanradius.html.
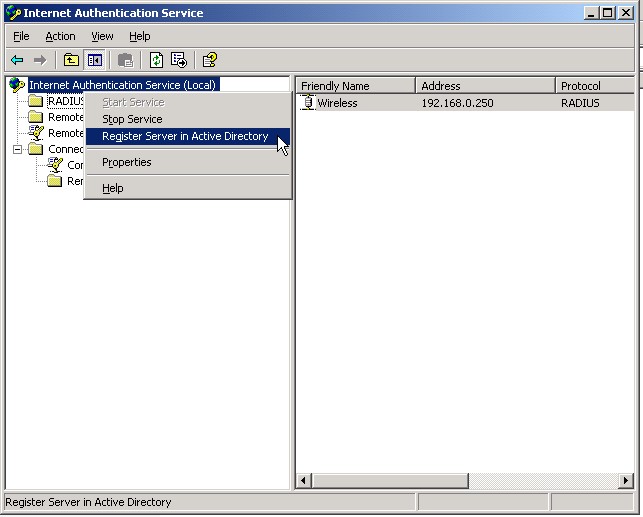
First of all you need to get your Certificate services setup. You also need to install Internet Authentication Service (IAS). In IAS you need to add a RADIUS client. Make sure the Messenger Authenticator Attribute is checked.

Next make sure you Authorize IAS in AD.
Next you’ll need to make a new Remote Access Policy. Use the wizard and make sure it has at least the NAS Port types shown below. This is also where it’s a good idea to specify a certain domain group that has access to the wireless. Then click Edit Profile and then click on the Authenication tab.

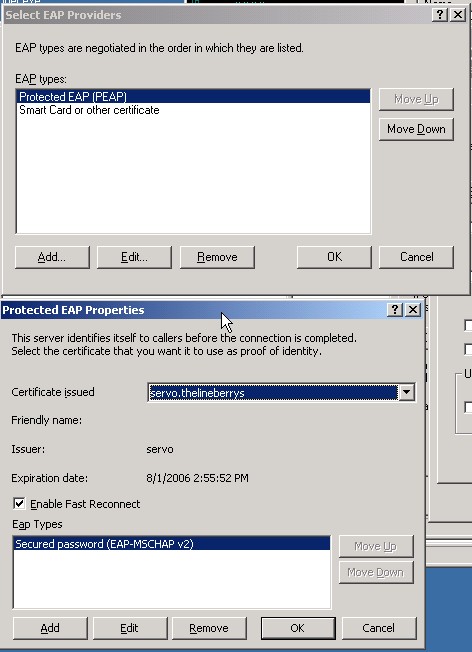
Then click on EAP Methods. PEAP is used if you just want to use Userid and passwords, add Smart Card or Certificate if you want to authenticate using certificates. If you plan on using PEAP make sure your settings are like that of below. Also make sure on both you select the correct server certificate.
That does it for the Server Setup.
Access Point Setup
All you have to do here is select WPA Radius or Radius. Enter your IAS Server’s IP address and the same passcode as you entered in the client setup in IAS.

Client Setup
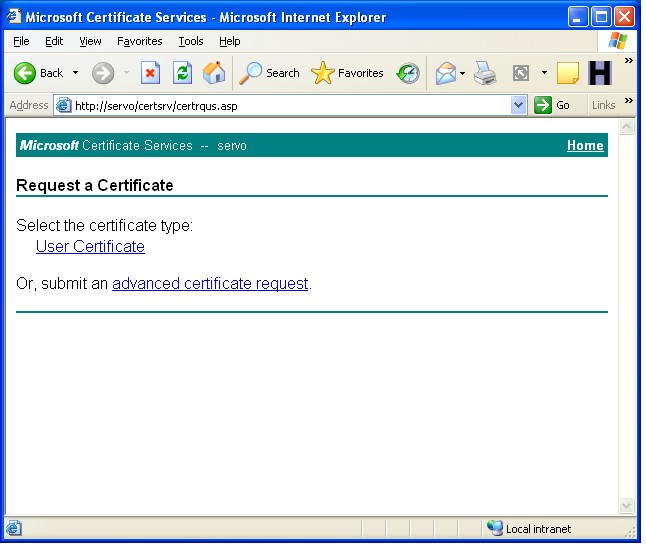
On the client side I use the Wireless Zero Configuration. The first thing you need to do is install the User Certificate from the server. You will need to connect to the trusted network probably through a direct ethernet connection. I have the ability to connect to my untrusted network and then VPN into the trusted network. Goto your server’s default website and then /certsrv/ as shown below. Click request certificate, then user certificate. Finish installing the certificate by following the rest of the directions.
Then open up you wireless configuration. Add the new wireless network, type in the SSID, Select WPA OR WEP (depending on what you set in the AP) and the same type of encryption you selected on the AP.

Next select whether you plan on using PEAP (authenticate using userid and password) or certificates (authenticate using certificates). Click properties. If you chose certificate then your next screen should look like the one below. Make your check boxes like mine, type in your full dns name for your server that is on it’s certificate into the connect to these servers field. Also make sure you select your server from the list of Trusted Root Certification Authorities.

That’s about it. You should now be able to connect to your wireles network. After I had it all setup and working, I turned off the SSID broadcast for the wireless. That means that no one else will even really know that this wireless network exists. This is completely secure because it requires that you be connected to the trusted network not on the wireless first to get the certificate, which means you should have access to the network. It also means that you need to have a AD userid and password. You don’t have to have your computer connected to the domain, just as long as the workgroup name is the same as the domain name and you use the same userid and password to log into windows as your AD userid and password. Also, since you are using WPA or WEP all your wireless data is encrypted.
